- Group structure
- Group visibility
- View groups
- View a group
- View group activity
- Create a group
- Edit group name, description, and avatar
- Leave a group
- Remove a group
- Remove a group immediately
- Restore a group
- Request access to a group
- View group members
- Filter and sort members in a group
- Add users to a group
- Remove a member from the group
- Add projects to a group
- Get the group ID
Groups
In GitLab, you use groups to manage one or more related projects at the same time.
You can use groups to communicate with all group members and manage permissions for your projects. If someone has access to the group, they get access to all the projects in the group.
You can also view all of the issues and merge requests for the projects in the group, and analytics about the group’s activity.
For larger organizations, you can also create subgroups.
For more information about creating and managing your groups, see Manage groups.
Group structure
The way to set up a group depends on your use cases, team size, and access requirements. The following table describes the most common models of structuring groups.
| Model | Structure | Use cases |
|---|---|---|
| Simple | One group for all your projects. | Work in a small team or on specific solutions (for example, a marketing website) that require seamless collaboration and access to resources. |
| Team | Different groups or subgroups for different types of teams (for example, product and engineering). | Work in a large organization where some teams work autonomously or require centralized resources and limited access from external team members. |
| Client | One group for each client. | Provide custom solutions for multiple clients that require different resources and access levels. |
| Functionality | One group or subgroup for one type of functionality (for example, AI/ML). | Develop complex products where one functionality requires specific resources and collaboration of subject-matter experts. |
Group visibility
Like projects, a group can be configured to be visible to:
- Anonymous users.
- All authenticated users.
- Only explicit group members.
The restriction for visibility levels on the application setting level also applies to groups. If set to internal, the explore page is empty for anonymous users. The group page has a visibility level icon.
Users cannot create a subgroup or project with a higher visibility level than that of the immediate parent group.
View groups
To explore all public groups you are a member of:
- On the left sidebar, select Search or go to.
- Select View all my groups.
- In the upper right, select Explore groups.
To view groups where you have direct or indirect membership:
- On the left sidebar, select Search or go to.
- Select View all my groups.
This page shows groups that you are a member of through:
- Membership of a subgroup’s parent group.
- Direct or inherited membership of a project in the group or subgroup.
View a group
The group overview page displays information about the group and its members, subgroups, and projects, such as:
- Group description
- Recent activity
- Number of merge requests and issues created
- Number of members added
- Subgroups and projects
- Shared projects
- Archived projects
To view a group:
- On the left sidebar, select Search or go to and find your group.
You can search for the subgroups and projects of the group and sort them in ascending or descending order.
View group activity
To view the activity of a group:
- On the left sidebar, select Search or go to and find your group.
- Select Manage > Activity.
-
Optional. To filter activity by contribution type, select a tab:
- All: All contributions by group members in the group and group’s projects.
- Push events: Push events in the group’s projects.
- Merge events: Accepted merge requests in the group’s projects.
- Issue events: Issues opened and closed in the group’s projects.
- Comments: Comments posted by group members in the group’s projects.
- Wiki: Updates to wiki pages in the group.
- Designs: Designs added, updated, and removed in the group’s projects.
- Team: Group members who joined and left the group’s projects.
Create a group
To create a group:
- On the left sidebar, at the top, select Create new () and New group.
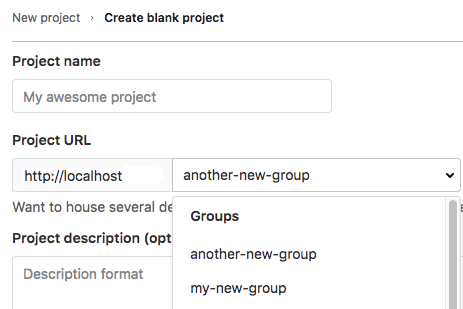
- Select Create group.
- In the Group name text box, enter the name of the group. For a list of words that cannot be used as group names, see reserved names.
- In the Group URL text box, enter the path for the group used for the namespace.
- Select the Visibility level of the group.
- Optional. To personalize your GitLab experience:
- From the Role dropdown list, select your role.
- For Who will be using this group?, select an option.
- From the What will you use this group for? dropdown list, select an option.
- Optional. To invite members to the group, in the Email 1 text box, enter the email address of the user you want to invite. To invite more users, select Invite another member and enter the user’s email address.
- Select Create group.
For details about groups, watch GitLab Namespaces (users, groups and subgroups).
Edit group name, description, and avatar
You can edit your group details from the group general settings.
Prerequisites:
- You must have the Owner role for the group.
To edit group details:
- On the left sidebar, select Search or go to and find your group.
- Select Settings > General.
- In the Group name text box, enter your group name. See the limitations on group names.
- Optional. In the Group description (optional) text box, enter your group description. The description is limited to 500 characters.
- Optional. Under Group avatar, select Choose file, then select an image. The ideal image size is 192 x 192 pixels, and the maximum file size allowed is 200 KB.
- Select Save changes.
Leave a group
- The button to leave a group moved to the Actions menu in GitLab 16.7.
When you leave a group:
- You are no longer a member of the group, its subgroups, and projects, and cannot contribute.
- All the issues and merge requests that were assigned to you are unassigned.
To leave a group:
- On the left sidebar, select Search or go to and find your group.
- On the group overview page, in the upper-right corner, select Actions ({ellipsis_v}).
- Select Leave group, then Leave group again.
Remove a group
- Enabled delayed deletion by default and removed the option to delete immediately on GitLab.com and on self-managed in GitLab 16.0.
To remove a group and its contents:
- On the left sidebar, select Search or go to and find your group.
- Select Settings > General.
- Expand the Advanced section.
- In the Remove group section, select Remove group.
- On the confirmation dialog, type the group name and select Confirm.
You can also remove a group from the groups dashboard:
- On the left sidebar, select Search or go to.
- Select View all my groups.
- Select () for the group you want to delete.
- Select Delete.
- In the Remove group section, select Remove group.
- On the confirmation dialog, type the group name and select Confirm.
In GitLab 12.8 and later, on GitLab Premium and Ultimate, this action adds a background job to mark a group for deletion. By default, the job schedules the deletion seven days in the future. You can modify this retention period through the instance settings.
In GitLab 13.6 and later, if the user who sets up the deletion is removed from the group before the deletion happens, the job is cancelled, and the group is no longer scheduled for deletion.
Remove a group immediately
- Introduced in GitLab 14.2.
- Enabled delayed deletion by default and removed the option to delete immediately on GitLab.com and on self-managed in GitLab 16.0.
If you don’t want to wait, you can remove a group immediately.
Prerequisites:
- You must have the Owner role for a group.
- You have marked the group for deletion.
To immediately remove a group marked for deletion:
- On the left sidebar, select Search or go to and find your group.
- Select Settings > General.
- Expand Advanced.
- In the Permanently remove group section, select Remove group.
- Confirm the action when asked to.
This action deletes the group, its subgroups, projects, and all related resources, including issues and merge requests.
Restore a group
- Introduced in GitLab 12.8.
To restore a group that is marked for deletion:
- On the left sidebar, select Search or go to and find your group.
- Select Settings > General.
- Expand the Advanced section.
- In the Restore group section, select Restore group.
Request access to a group
As a user, you can request to be a member of a group, if an administrator allows it.
- On the left sidebar, select Search or go to.
- Select View all my groups.
- In the upper right, select Explore groups.
- In the Search by name text box, enter the name of the group you want to join.
- In the search results, select the name of the group.
- On the group page, under the group name, select Request Access.
Up to ten of the most recently active group owners receive an email with your request. Any group owner can approve or decline the request.
If you change your mind before your request is approved, select Withdraw Access Request.
View group members
To view the direct and inherited members of a group:
- On the left sidebar, select Search or go to and find your group.
- Select Manage > Members.
A table displays the member’s:
- Account name and username.
- Source of their membership. For transparency, GitLab displays all membership sources of group members. Members who have multiple membership sources are displayed and counted as separate members. For example, if a member has been added to the group both directly and through inheritance, the member is displayed twice in the Members table, with different sources, and is counted as two individual members of the group.
- Max role in the group.
- Expiration date of their group membership.
- Activity related to their account.
To view all namespace members (and their respective occupied seats), in the top-level namespace, view the Usage Quotas page.
Filter and sort members in a group
- Introduced in GitLab 12.6.
- Improved in GitLab 13.7.
- Feature flag removed in GitLab 13.8.
To find members in a group, you can sort, filter, or search.
Filter a group
Filter a group to find members. By default, all members in the group and subgroups are displayed.
In lists of group members, entries can display the following badges:
- SAML, to indicate the member has a SAML account connected to them.
- Enterprise, to indicate that the member of the top-level group is an enterprise user.
- On the left sidebar, select Search or go to and find your group.
- Select Manage > Members.
- Above the list of members, in the Filter members text box, enter your search criteria. To view:
- Direct members of the group, select Membership = Direct.
- Members of the group and its subgroups, select Membership = Inherited.
- Members with two-factor authentication enabled or disabled, select 2FA = Enabled or 2FA = Disabled.
- Members of the top-level group who are enterprise users, select Enterprise = true.
Search a group
You can search for members by name, username, or public email.
- On the left sidebar, select Search or go to and find your group.
- Select Manage > Members.
- Above the list of members, in the Filter members box, enter search criteria.
- To the right of the Filter members box, select the magnifying glass ().
Sort members in a group
You can sort members by Account, Access granted, Max role, or Last sign-in.
- On the left sidebar, select Search or go to and find your group.
- Select Manage > Members.
- Above the list of members, in the upper-right corner, from the Account list, select the criteria to filter by.
- To switch the sort between ascending and descending, to the right of the Account list, select the arrow ( or ).
Add users to a group
- Expiring access email notification introduced in GitLab 16.2.
You can give a user access to all projects in a group.
Prerequisites:
- You must have the Owner role for the group.
- On the left sidebar, select Search or go to and find your group.
- Select Manage > Members.
- Select Invite members.
-
If the user:
- Has a GitLab account, enter the user’s username.
- Doesn’t have a GitLab account, enter the user’s email address.
- Select a default role or custom role.
-
Optional. For Access expiration date, enter or select a date. From that date onward, the user can no longer access the project.
If you enter an access expiration date, the group member gets an email notification seven days before their access expires.
If you give a member the Maintainer role and enter an expiration date, that member has full permissions as long as they are in the role. These permissions include the member’s ability to extend their own time in the Maintainer role. -
Select Invite. If you invite the user by their:
- GitLab username, the user is added to the member list.
- Email address, the user receives an email invitation and is prompted to create an account. If the invitation is not accepted, GitLab sends reminder emails two, five, and ten days later. Unaccepted invites are automatically deleted after 90 days.
Members that are not automatically added are displayed on the Invited tab. This tab includes users who:
- Have not yet accepted the invitation.
- Are waiting for approval from an administrator.
- Exceed the group user cap.
Remove a member from the group
Prerequisites:
- You must have the Owner role.
- The member must have direct membership in the group. If membership is inherited from a parent group, then the member can be removed from the parent group only.
To remove a member from a group:
- On the left sidebar, select Search or go to and find your group.
- Select Manage > Members.
- Next to the member you want to remove, select the vertical ellipsis ().
- Select Remove member.
- Optional. On the Remove member confirmation dialog, select one or both checkboxes:
- Also remove direct user membership from subgroups and projects
- Also unassign this user from linked issues and merge requests
- Select Remove member.
GitLab administrators can also ensure removed users cannot invite themselves back.
Add projects to a group
You can add a new project to a group in two ways:
- Select a group, and then select New project. You can then continue creating your project.
-
While you are creating a project, select a group from the dropdown list.
Specify who can add projects to a group
By default, users with at least the:
- Developer role can create projects under a group. This default can be changed.
- Maintainer role can fork projects into a group. This default prevents users with the Developer role from forking projects that contain protected branches and cannot be changed.
To change the role that can create projects under a group:
- On the left sidebar, select Search or go to and find your group.
- Select Settings > General.
- Expand the Permissions and group features section.
- From Roles allowed to create projects, select an option.
- Select Save changes.
To change this setting globally, see Default project creation protection.
Get the group ID
- Group ID moved to the Actions menu in GitLab 16.7.
You might need the group ID if you want to interact with it using the GitLab API.
To copy the group ID:
- On the left sidebar, select Search or go to and find your group.
- On the group overview page, in the upper-right corner, select Actions ({ellipsis_v}).
- Select Copy group ID.